Waarp R66-Configuration
The primary installation of a server is done using the following steps:
|
|
|
|
|
|
|
|
|
|
Below those several steps are illustrated.
Note that the various tools are consolidated into one GUI named : Central Administrator (Xml Editor, Password, R66Gui) plus some other functions.
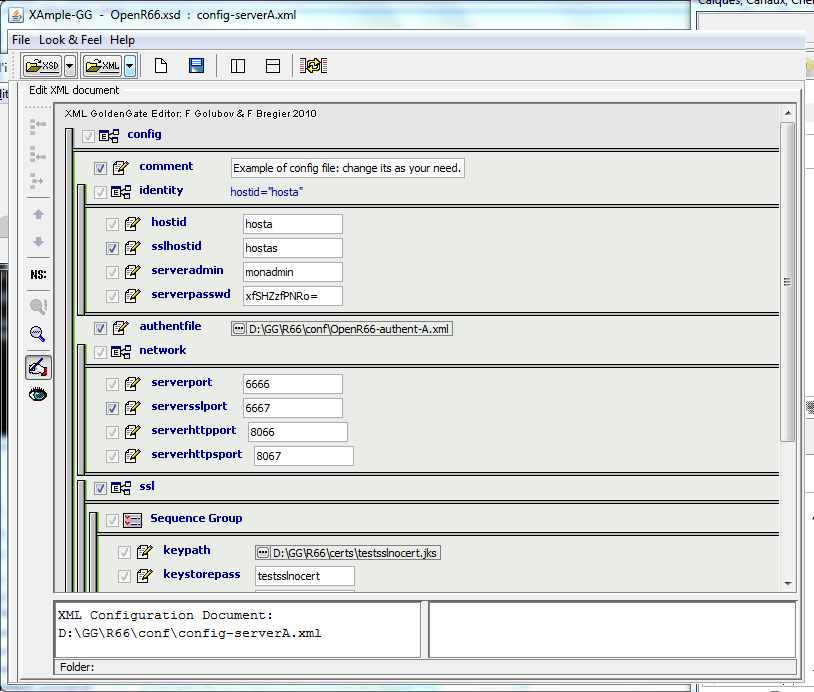
2) XML Configuration
To configure a Waarp R66 Server, you need to first create the XML files as needed (see the Xml Config files page): main config file, authent file, rules and limit config files. To help the administrator to generate correct files, XSD models are defined to be used with an extension of the project Xample (XML Gui Editor) from Felix Golubov.
Note that the httpadmin shall specify the correct path for your choice of Waarp HTTPS/HTTP administrator/supervision tool. Now the default is i18n support based.
It is also possible to use JAXE with jaxe-xxx-config.xml files.
3) Password configuration
For the administrator you need a specific DES Key for the crypted password support. DES crypted support and generation are available through the GoldenGate Password GUI project.
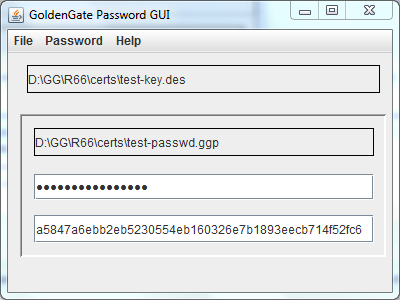
Note that under Mainframe, some people reports that adding -Dfile.encoding=UTF8 fixes some issues with passwords.
4) Cryptography
For the administrator you need a KeyStore containing a RSA key for SSL support in HTTPS.
You need another KeyStore for the SSL support in the Waarp R66 protocol, but only if you want to use this SSL channel.
If you don't want that OpenR66 uses SSL between two hosts, then you only need one KeyStore for the HTTPS support.
In the source, you will find in the certs directory 2 such keystore named admin66.store and openr66.store. You can named the files as you wanted (using the standard "jks" extension for instance).
To generate those files, you can also ue the keytool command from the jdk, or using the cool free tool KeyTool IUI (last known version in 2.4.1).
For instance: keytool -genkey -alias myalias -keyalg RSA -validity xxx -keystore mystore.store
Below you will find the full detail on how to create those KeyStore and TrustedKeyStore according to your needs:
To generate the stores for Waarp R66 for instance, you need to create 2 JKS keyStore. To generate those files, you can use the "keytool" command from the JDK or using the free tool KeyTool IUI (last known version in 2.4.1). Below we show how to use the Keytool IUI.
Then you have to fill the ports to use (serverssl port for Waarp R66 channels, serverhttpsport for the administrator) and to set up the good path to every components (don't forget the path to the html admin files, between admin or admin2 - the second being more dynamic - ).
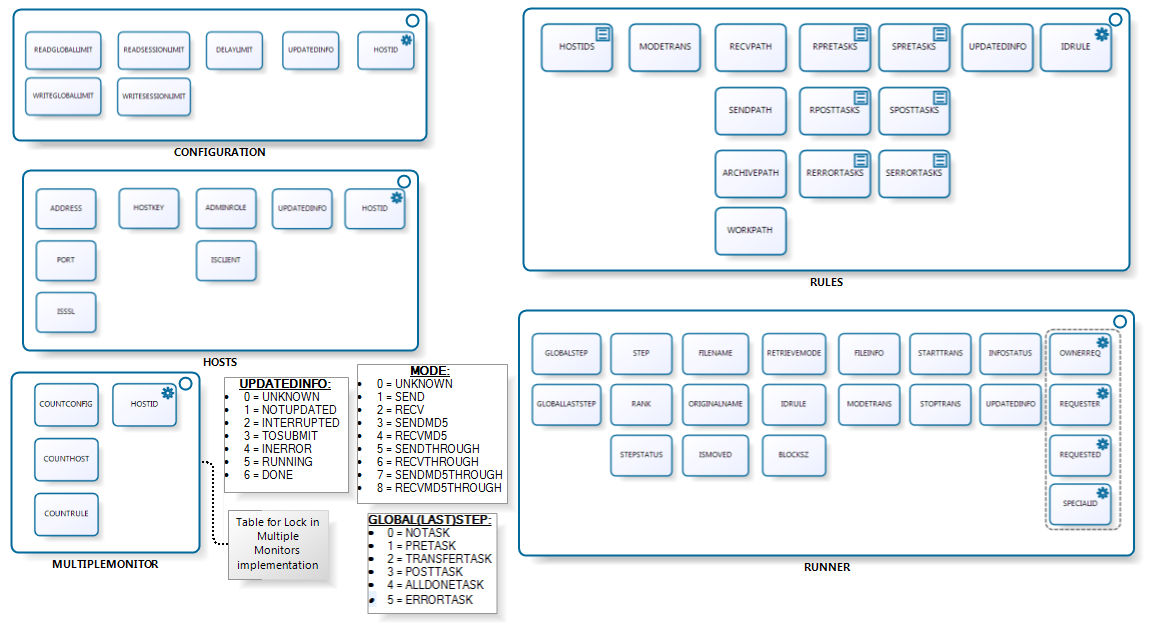
7) Database configuration
Then, you create a database entry in the model you choose (currently supported is Oracle, PostGreSQL, MySQL and H2 Database). This database entry should be referenced in the XML config files. Below is presented the schema of the database that will be created.
You need to get all the necessary jar (see the depencies of the project) to allow you to launch the server. An example of shell script including all jar is presented in the src/main/example directory.
Then you launch the ServerInitDatabase.
Note that multiple Waarp R66 Servers may shared the exactly same database. Waarp R66 is compatible with such a model. Note however that Rules are strictly shared, which means that you will need to take care of the absolute path of EXEC commands such that they are valid on all Waarp R66 servers where it should be executed.
Note also that from version 2.4.17, it is possible to update the database schema using ServerInitDatabase -updateDb.
8) Example of logback.xml file
<configuration>
<appender name="FILE"
class="ch.qos.logback.core.rolling.RollingFileAppender">
<file>/GG/R66/log/R66Server.log</file>
<append>true</append>
<rollingPolicy class="ch.qos.logback.core.rolling.TimeBasedRollingPolicy">
<fileNamePattern>/GG/R66/log/R66Server.%d{yyyy-MM-dd}.%i.log.zip</fileNamePattern>
<maxHistory>30</maxHistory>
<timeBasedFileNamingAndTriggeringPolicy class="ch.qos.logback.core.rolling.SizeAndTimeBasedFNATP">
<maxFileSize>10MB</maxFileSize>
</timeBasedFileNamingAndTriggeringPolicy>
</rollingPolicy><encoder class="ch.qos.logback.classic.encoder.PatternLayoutEncoder">
<pattern>
%date{dd/MM/yyyy/HH:mm:ss.SSS} %level [%logger] [%thread] %msg%n
</pattern>
</encoder>
</appender><appender name="STDOUT"
class="ch.qos.logback.core.ConsoleAppender">
<encoder class="ch.qos.logback.classic.encoder.PatternLayoutEncoder">
<Pattern>%date{dd/MM/yyyy/HH:mm:ss.SSS} %level [%logger] [%thread] %msg%n</Pattern>
</encoder>
</appender>
<root>
<level value="warn" />
<appender-ref ref="FILE" />
<appender-ref ref="STDOUT" />
</root>
</configuration>And use the -Dlogback.configurationFile=J:/GG/R66/conf/logback.xml as argument to the java command (before the class to launch, roughly were you put the -Xms -Xmx arguments).
9) Extra Waarp JVM Options
Moreover, several options can be placed in the command line (preferably in ENV_R66 or setvari.bat):
-Dopenr66.startup.checkdb=1|0 to choose if database configuration shall be checked at startup (default is true)
-Dopenr66.filename.maxlength=n (default n = 255) to choose the default max filename length used when receiving a file (for the temporary filename and final filename). This does not prevent to change the filename after (and #ORIGINALFILENAME# does still contain the full filename, untroncated).
-Dopenr66.trace.stats=n (default n=0) to debug by making a trace of some specific data structure usages every n s, where n is specify as value in the definition. If 0 or less, means not activated.
-Dopenr66.cache.limit=n and -Dopenr66.cache.timelimit=m (default n=20000, m=180000 - 180s -) to manage the cache behavior of Transfer informations with
n being the maximum number of DbTaskRunners to keep in LRU cache (used in self request and for instance without database) - Minimal value is 100 -
m being the maximum time in ms of valid element once created, used or updated (used in self request and for instance without database). - Minimal value is 1000 ms (1s). If set to 1000, the value will not be regularly cleaned of outtimed values but the cache will be filled up to n. -
Now you can launch the Waarp R66 Server.
Note that you can add specific user rights with specific authentication to access to the Web administrator interface from version 2.4.22 (see here), in addition to the super user specified in the XML configuration file of the server.